AI-generated summary
In today’s information society, every environment functions as an “information environment,” heavily reliant on data and metadata that underpin activities across sectors such as industry, services, mobility, and health. The global big data market is projected to expand significantly, reflecting this dependence. While data enables faster, personalized, and more efficient operations, it also introduces vulnerabilities, particularly in cybersecurity. To ensure systems work safely and effectively, the concept of “infostructure”—a synergy of human and machine collaboration treating information as a valuable asset—is crucial. Protecting data confidentiality, integrity, and accessibility is paramount, as cyberattacks can disrupt critical services like transportation and healthcare, with real-world examples including ransomware attacks on the UK’s NHS and American medical device manufacturers.
The rise of IoT devices intensifies these risks, with billions of connected devices worldwide, projected to increase dramatically by 2025. Cybercrime, especially ransomware, poses enormous financial threats, potentially ranking as the world’s third-largest economy. Challenges such as weak regulations, rapid market growth, technical limits, user ignorance, insufficient corporate incentives, and lack of standards complicate cybersecurity efforts. Although the European Union has introduced regulatory frameworks, effective protection demands a comprehensive approach integrating technology, policies, risk management, legal measures, employee training, and a strong data culture. Human error remains a major cause of security breaches, emphasizing the need for education and training to develop a holistic understanding that leverages opportunities while mitigating risks in the information society.
Beyond the technical aspects, ensuring the confidentiality, integrity, and accessibility of data depends on a shared skill set and knowledge.
In the information society, any environment is an ‘information environment’. The global big data market is expected to grow from $162.6 billion in 2021 to $273.4 billion in 2026, according to Market Data Forecast. But, beyond numerical analysis, it is the day-to-day that shows us the importance of data and metadata, on which most of our activities are based: from industry to services, from mobility to health.
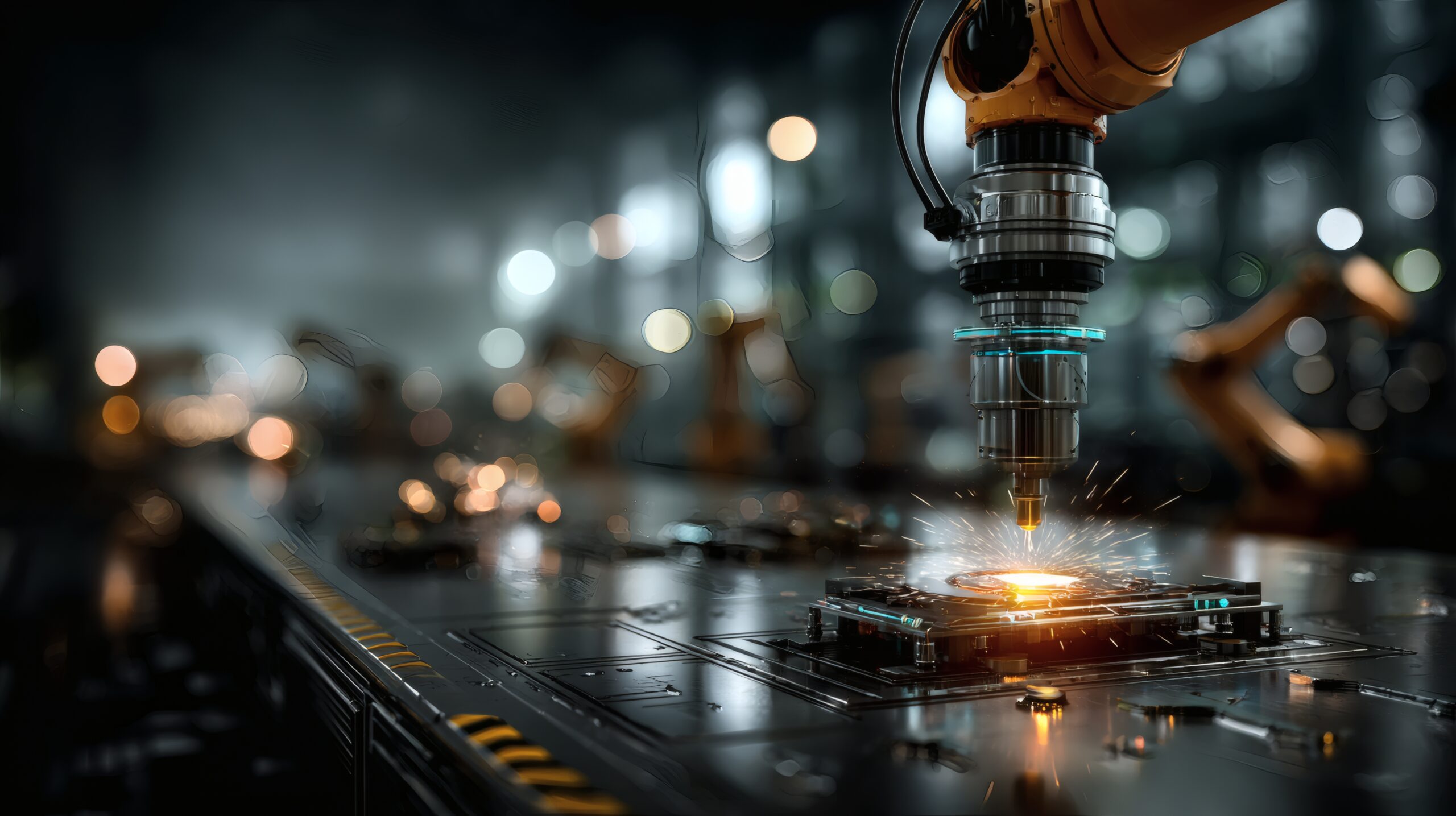
The dependence on data, in addition to ensuring better, faster and personalized performance in almost all fields, also exposes us to vulnerabilities related to computer security. For everything to work efficiently and safely, the concept of infrastructure must be combined with that of ‘infostructure’: the result of humans and machines working together to consider information not as a tool, but as an asset in itself.
The priority, as pointed out by the Bankinter Innovation Foundation’s Megatrends 2023, is to ensure the confidentiality, integrity and accessibility of the data. In fact, what if someone took control of highway panels, giving wrong directions and paralyzing traffic? The mobility sector, like the healthcare sector, is not immune to cyber threats and risks: attacks happen every day and can have a devastating impact on the economy and people’s health.
In 2022, the British public health system (NHS) suffered the consequences of a ransomware attack on a provider. Ambulance shipments, emergency prescriptions and access to the records of thousands of patients were affected. The most intimate data of thousands of citizens, exposed. On the other hand, St. Jude Medical, an American medical device company, was attacked in 2017 by cybercriminals who gained access to patients’ pacemakers.
This type of vulnerability will increase with the expansion of IoT devices, which are already present in virtually every aspect of our lives. Research by IoT Analytics shows that IoT connections, such as home automation devices, connected vehicles and industrial equipment, already accounted for 54% of the 21.7 billion active connected devices in 2020, estimating that by 2025 there will be more than 30 billion IoT connections, about four devices for every inhabitant of the planet.
The World Economic Forum’s (WEF) State of the Connected World 2023 quantifies the global financial impact of ransomware attacks: $7,000 trillion in 2022, a figure that would make cybercrime the world’s third-largest economy after China and the United States. Among the criticalities that governments along with all IoT supply chain operators are called upon to address, the WEF mentions:
- Underdeveloped regulatory frameworks.
- Rapid expansion of markets and companies in the IoT sector and related technologies.
- Technical limitations.
- Lack of knowledge of end users.
- Insufficient incentives for companies to protect users.
- Lack of standardization.
The European Union has published a series of regulations that, however, still need to be implemented and harmonized by states: from the Cyber Resilience Act to the NIS2 Directive, including the DORA regulation. The fact is that the protection, accessibility, and correct use of data in the context of the infostructure is not just a matter of cybersecurity practices, it is the set of tools, company policies, risk management approaches, legal guidelines, employee training, and technologies used.
Statista shows that 33% of companies that have adopted IoT consider security issues related to a lack of skilled personnel as the most critical concern for the corporate ecosystem. A concern that has increased with remote work, with many operators relying on home networks and personal devices to perform their tasks. In addition, the vast majority of cyberattacks have their origin in a breach opened by a third party: suppliers, subcontractors or consultancies.
Today, when everything is so liquid and permeable, without full perception at the systemic level, it becomes impossible to manage the various resources and nodes of the chain. IT infrastructures arise from the perfect balance between hardware and software and are the engine of organizations, which, through the correct use of the data collected, feed the world economy. However, the vast majority of computer security incidents do not depend on the robustness of the infrastructure, but are caused by human error and its incorrect and potentially dangerous practices.
Thus, an effective infostructure is made up of material and intangible elements, which combine the available information, the software used for its organization in the system, the policies for its appropriate use (such as the General Data Protection Regulation: GDPR) and the human component that manages it; It concerns the way in which information, documents, goods and services are organized within complex spaces to favor their orientation, findability, usability and comprehensibility.
This infostructure must be built on technologies and skills—networking, processing, standards, executable rules, and business models—that contribute to the protection, availability, and use of information. All this thanks to a block of knowledge and good practices with which to cement a solid data culture.
That is why it is necessary to invest in education and training that allows a holistic vision capable of taking advantage of the opportunities offered by the information society, without incurring the associated risks.